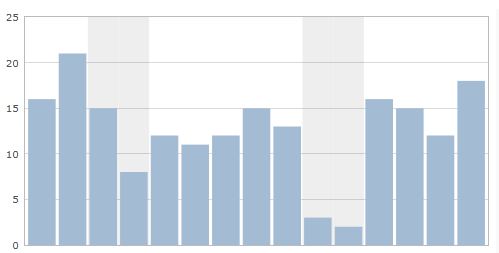
Below are examples of metrics and measures that are common when looking at IT infrastructure, middleware, and server performance. Why People Use These Metrics These metrics are useful when: Considering service level metrics for infrastructure hosting providers and applications. What to charge clients based on usage of infrastructure services. Quality, stability, and capacity of infrastructure services… Continue reading Service Level Metrics for Middleware and Server Performance Monitoring
Month: March 2011
Removing viruses, trojans, and other malware from your Windows computer
These steps are easy when you know exactly when your Windows computer has been infected (e.g. inserting a USB stick, visiting a website with malicious software on your browser). At the time of infection or shortly after infection, perform the following steps: Immediately turn off your computer and unplug it from the network / internet (remove the… Continue reading Removing viruses, trojans, and other malware from your Windows computer
Helpful GIMP Tips and Tutorials
About GIMP and Inkscape GIMP is a raster/bitmap graphics tool and Inkscape is a vector graphics tool. Together they meet most graphics needs in photo/image manipulation and creation of scalable graphics and offer free/open source alternatives to Adobe Photoshop and Illustrator. Answers to Common Questions on: Drawing simple shapes Layer manipulation Combining images and photos Application… Continue reading Helpful GIMP Tips and Tutorials